Originally Posted by
chagzuki
I wonder how it took them by surprise. I mean, if it's that easy to pick the lock then the mechanism must be extremely simple and it's ineffectuality obvious.
This is an easy question for hackers to answer.
Imagine you're sitting in a room with a lot of well-seasoned (say in their 30s, 8-ish years of experience), degree-carrying, highly-trained computer security experts. They know what they're doing. They hammer you with best practices. They complain about compliance. They write security policies for tons and tons of systems. They give you Acceptable Use Policies and Patch Management Policies.
A new worm comes out.
They all panic.
Reports on the worm are found, examined. Services that it crashes to get in are blocked. IDS signatures go in. AV signature gets updated.
Now, you look at the worm, you go, "Watch this..."
Pull open a terminal, run a few commands. Echo some escape sequence, $(perl -e puts "A" x 1000), payload... you get a shell. Add a local admin account, exit the shell and crash a critical service on the remote end, and the system reboots. Now RDP in with that new account, and have shiny admin access.
Watch all your security guys turn white.
They really have absolutely no clue what they're doing. Security people study security. They study how to make things secure. The problem is they don't understand how to break things; they know that X is a security best practice and Y is a problem you look for, end of story.
Lock manufacturers knew locks could be picked, end of story. They found a different style of lock, something that doesn't have the same vulnerabilities. That's what's obvious: it's different, and doesn't have these vulnerabilities.
Locksmiths and lock hackers, on the other hand, are different. People like me don't play by the rules; we look for things that are stupid, irrelevant, or forbidden. Did you know pin tumbler locks use a number of 2 piece shafts cut from brass to block the rotation of the lock?
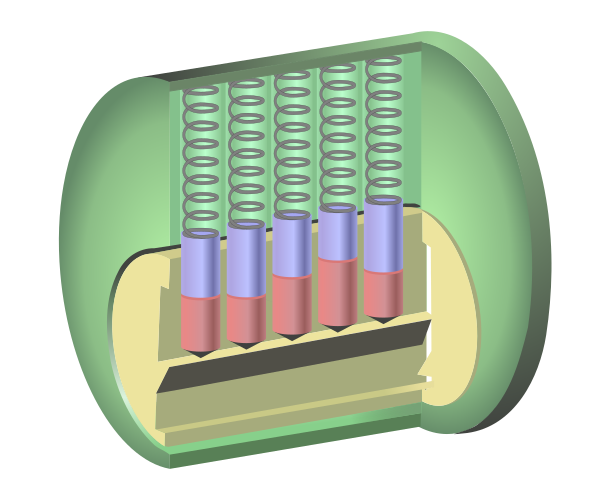
When you put in the key, the shafts raise; raise each shaft to the right height and the border between the rotating barrel and its housing lines up with the split in the pin, rather than blocking against one of the two pieces.
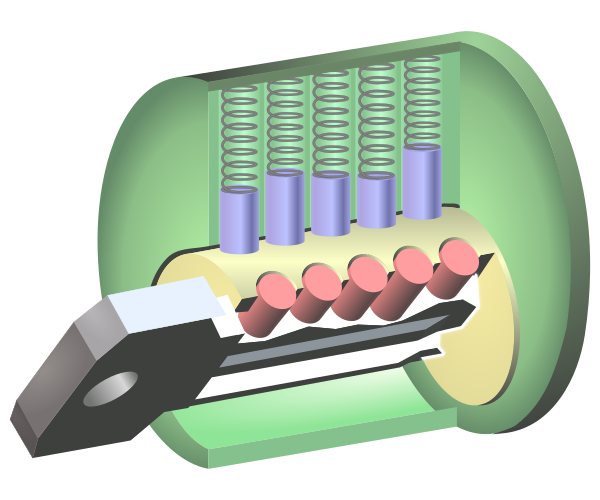
Well, these pins are cut from a rod of brass; the cut ends of the pins are not polished; and unpolished things have a lot of drag. Torque the barrel, raise the pins, then let them slip just enough... the lower pin drops out, the upper pin stays caught along the housing, and the barrel rotates.
This attack isn't part of the design. Nobody designed these locks to operate properly with the barrel torqued against the pins and the pins torqued against the housing. Never mind some freakish act where you nudge the pins around, then allow them to slip down, but with some unspecified, unmeasured, unpredicted, and inconsistent amount of torque that's enough to trap the jagged edge of the upper pin, but not hold it in place just by friction with the pin body. That's all black magic.
I don't play by the rules; my first thought when I see something is "how do I break it?" Why should I believe anyone else does? You don't make anything secure by designing it to be secure; you make it secure by designing out any and all unpredicted modes of operation.